This pathway is a strong fit for students who:
- Have a curiosity to explore how things work and experiment with problem-solving solutions to secure them (sometimes by breaking them).
- Enjoy solving spatial puzzles and are intrigued by the prospect of outsmarting adversaries.
- Have a passion for technology and software systems.
- Are interested in psychology and profiling human behavior.
- See themselves managing agile human and AI teams responsible for securing systems.
- Are interested in the intersection of human behavior and technology.
- Believe in the importance of privacy and security in our digital age.
Example Occupations and Common Fields
Example occupations:
- Cybersecurity Analyst
- Behavioral Analyst (Cybersecurity)
- Information Security Engineer
- Cyber Threat Intelligence Specialist
- Cyber Operations Planner
- Cybersecurity Risk Analyst
- Cybersecurity Consultant
- Incident Response Specialist
- Security Systems Engineer
Common fields:
- Information technology
- Health Systems
- Finance
- Healthcare
- Cybersecurity firms
- Military
- Government agencies
- Aerospace
- Defense
Courses and Experiences
- IND E 351: Human Factors in Design
- IND E 455: User Interface Design
- INFO 103: Social Media, Ethics, and Automation
- INFO 310: Information Assurance and cybersecurity
- CSE 154: Web Programming
- CSE 412: Introduction of Data Visualization
- CSE 416: Introduction to Machine Learning
- CSE 484: Undergraduate Computer Security
- IND E 499: Research/Independent Study w/Prashanth
Frequently Asked Questions
Do I need a graduate degree specializing in this area to be marketable to the field?
No, many roles in cybersecurity value hands-on experience, certifications, and foundational understanding. However, a specialized graduate degree can open doors to advanced roles and research opportunities in the field.
What are some examples of real-world areas of application?
Real-world applications for the Cybersecurity Pathway include:
- Threat Detection: Using behavioral patterns to detect potential threats in real-time.
- Secure System Design: Designing software and infrastructure resistant to cyber-attacks.
- Fraud Prevention: Identifying anomalous patterns in financial transactions to prevent fraud.
- Privacy Protocols: Developing protocols that ensure data privacy for users.
- Incident Response: Creating strategies to respond to and mitigate the effects of cyber breaches.
Does this pathway touch on global impact, equity and/or quality of life?
Yes, it does. Cybersecurity has a direct global impact, as cyber threats and privacy concerns are universal challenges. By creating more secure systems, we're ensuring equitable access to safe digital spaces for everyone, irrespective of their location. Moreover, by emphasizing the importance of privacy and security in our digital age, this pathway contributes to enhancing the quality of life by fostering trust and safety in online interactions and transactions.
From Classroom to Career: Alumni Spotlight
See how our remarkable alumni are using their ISE degrees in this field.

Viggo Forde
CIO for Snohomish County
My passion is to help lead transformation projects that make teams and businesses more successful.
As a certified Prosci Change Management leader I can successfully step into transformation projects large and small. My work has shaped how teams look and operate and the outcomes have resulted in measurable customer and business impacts. This experience spans multiple lines of business and companies.
In the last two years my core focus has been on leading technology modernization and a large portfolio of IT systems and infrastructure for Snohomish County Government with 3000 employees. Prior to that I led large transformation projects in Customer Service and Support at Microsoft that impacted how the global support business operates. These projects led to dramatic improvements for customer and employees both.
My leadership experience spans three multinational companies with deep subject matter expertise in global information and content management, program management, and technical / customer support strategies. This is supported by an ability to lead effective change management in a highly matrixed and distributed stakeholder environment.
Using insights gained from data and analysis I have successfully managed complex businesses and organizations. Data-driven decision making helps me achieve higher impact.
I have a collaborative leadership style and as a manager and leader have demonstrated the ability to hire and create successful teams that drive impacts in global organizational structures.
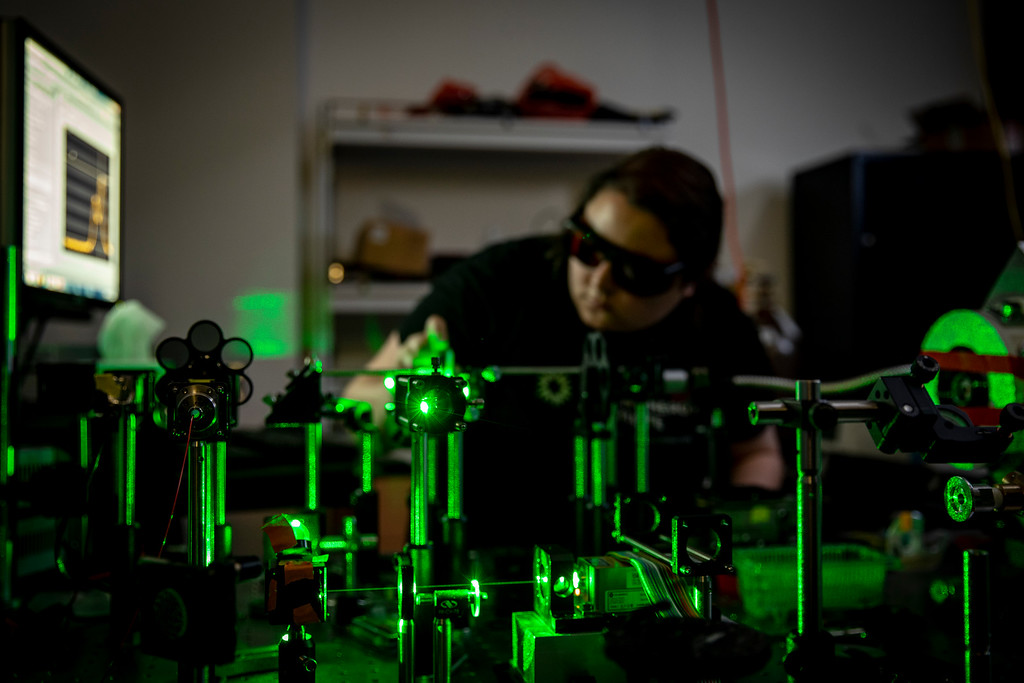
Behavioral Research in Information and Computer Security (BRICS) Laboratory
At the BRICS Lab, Assistant Professor Prashanth Rajivan and his research group are working on problems at the intersection of human factors and cyber security to understand the social and cognitive processes that people use to detect malicious signals online. This includes studying the cognitive processes associated with the detection of phishing emails and misinformation on social media platforms.